vuLnDAP
vuLnDAP is a vulnerable LDAP based web app written entirely in Golang. The project is a response to a request from Adrien who said he'd like a vulnerable LDAP server for his SANS 642 class. As I've never really used either Golang or LDAP before I though it would be a good time to learn both. Because of this, the Go code is probably not the best and the LDAP interaction maybe not quite the way it would be done in the real world but hopefully it will give you a good idea on ways to exploit it.
The project is hosted on GitHub.
Background
Before I started writing the tool I read up on common attacks against LDAP and found that a lot of them no longer work due to an update/fix that went into the query parsing engine which blocked the most common attack which was the equivalent of the SQL or 1=1 injection. Because of this, I wanted to put something together that used LDAP in the way it expected to be used and was vulnerable to business logic flaws rather than code vulnerabilities.
Installation
There are three ways to use the app...
Use My Copy
If you don't want to bother doing a custom installation then I'm running a copy of the site on the URL vulndap.digi.ninja. I'm not logging anything other than the standard Apache web logs but may change this if I start seeing some interesting attacks coming through.
Please don't abuse this, the vulnerabilities are in the application, you won't get anything from port scans or hitting it with Nessus.
Binaries
When I push source to the master branch I'll also try to make sure I build binaries for x86, amd64 and possibly OSX although I've no way to test this so report any problems. The binaries will be in the bin directory and can be ran in the same way as any other binary, there should be no dependencies. These will be in the bin directory and given obvious names.
Run From Source
These instructions are for building on a Debian based system (Debian, Ubuntu, Kali etc), if you want to build in other environments then you are on your own, this is the only environment I've got to work with.
Being a Golang app, vuLnDAP first requires Go to be installed:
apt-get install golangYou can now get a copy of the source using the following command:
go get github.com/digininja/vuLnDAPUnless you've customised your Go environment, this will install the app into ~/go/src/github.com/digininja/vuLnDAP.
You now need to install the dependencies:
cd ~/go/src/github.com/digininja/vuLnDAP
go get -d ./...Finally you can build the app:
go buildThe last thing you need to do is to create yourself a config file, the easiest way to do this is to copy the sample file across and use the defaults:
cp vulndap.cfg-sample vulndap.cfgThis will create the vuLnDAP binary in the current directory which you run as any other binary:
$ ./vuLnDAP
INFO[0000] Main App Started Owner=Main
INFO[0000] Client Started Owner=Client
DEBU[0000] Dumping configuration information Owner=Config
DEBU[0000] Web server listening on: 0.0.0.0:9090 Owner=Config
DEBU[0000] Connecting to LDAP server on: localhost:10389 Owner=Config
DEBU[0000] BaseDN: dc=hack,dc=me Owner=Config
DEBU[0000] Using credentials: cn=robin,ou=admins,dc=hack,dc=me / hello Owner=Config
DEBU[0000] Debug mode: true Owner=Config
INFO[0000] Starting LDAP server Owner=Main
DEBU[0000] Sleeping for 500ms to give the server time to start up Owner=Main
INFO[0000] Server started Owner=Server
INFO[0000] LDAP server listening on localhost:10389 Owner=Server
INFO[0000] Binding to LDAP server Owner=Main
INFO[0000] Binding to localhost:10389 Owner=Client
DEBU[0000] Bind request as cn=robin,ou=admins,dc=hack,dc=me from 127.0.0.1:49916 Owner=Server
DEBU[0000] Bind success as cn=robin,ou=admins,dc=hack,dc=me from 127.0.0.1:49916 Owner=Server
INFO[0000] Starting web server on 0.0.0.0:9090 Owner=ClientUsage
Assuming you are using the default config file you can now browse to the app on port 9090 and the LDAP server will start up on port 10389.
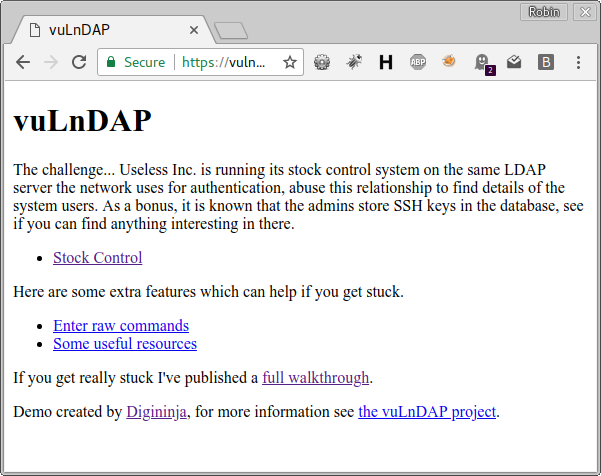
The app has three sections, a vulnerable stock control system, a feature to allow raw LDAP queries (useful for debugging and testing) and a page of resources. The scenario is that the stock control system is built on the same LDAP database used by the company for network user management, the goal is to dump a copy of the users with an additional goal of acquiring a set of useful SSH keys. As far as I know, this will require chaining a number of issues together however, if you know what you are doing with LDAP queries, you may be able to do it in a single step.
If you get really stuck, I've done a full walkthrough.
The LDAP server is a very cut down one so can't be accessed with things like phpLDAPadmin but you can talk to it using ldapsearch:
$ ldapsearch -xb '' -h localhost -p 10389 -D cn=robin,ou=admins,dc=hack,dc=me -w SteelConRocks -b dc=hack,dc=me 'objectclass=Fruits' name description
# extended LDIF
#
# LDAPv3
# base with scope subtree
# filter: objectclass=Fruits
# requesting: name description
#
# banana, fruits, hack.me
dn: cn=banana,ou=fruits,dc=hack,dc=me
description: yellow and bendy
# apple, fruits, hack.me
dn: cn=apple,ou=fruits,dc=hack,dc=me
description: red and juicy
# search result
search: 2
result: 0 Success
# numResponses: 3
# numEntries: 2

